[ad_1]

The software program framework has turn out to be important to growing virtually all complicated software program today. The Django Net framework, as an example, bundles all of the libraries, picture recordsdata, and different parts wanted to rapidly construct and deploy net apps, making it a mainstay at firms like Google, Spotify, and Pinterest. Frameworks present a platform that performs widespread features like logging and authentication shared throughout an app ecosystem.
Final week, researchers from safety agency Intezer revealed the Lightning Framework, a modular malware framework for Linux that has gone undocumented till now. Lightning Framework is post-exploit malware, which means it will get put in after an attacker has already gained entry to a focused machine. As soon as put in, it may well present a number of the similar efficiencies and pace to Linux compromises that Django supplies for net growth.
“It’s uncommon to see such an intricate framework developed for focusing on Linux methods,” Ryan Robinson, a safety researcher at Intezer, wrote in a post. “Lightning is a modular framework we found that has a plethora of capabilities, and the power to put in a number of forms of rootkit, in addition to the aptitude to run plugins.”
Intezer
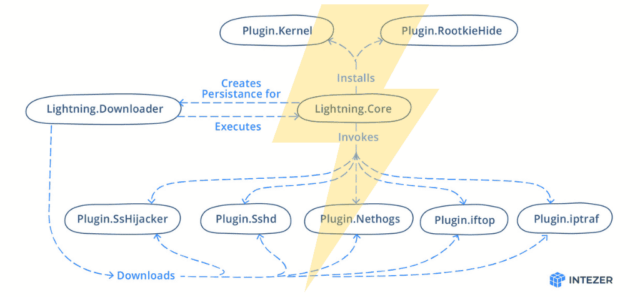
Lightning consists of a downloader named Lightning.Downloader and a core module named Lightning.Core. They connect with a delegated command and management server to obtain software program and obtain instructions, respectively. Customers can then run any of a minimum of seven modules that do every kind of different nefarious issues. Capabilities embrace each passive and lively communications with the menace actor, together with opening a safe shell on the contaminated machine and a polymorphic malleable command.
The framework has each passive and lively capabilities for communication with the menace actor, together with opening up SSH on an contaminated machine, and help for connecting to command and management servers that use malleable profiles. Malware frameworks have existed for years, however there aren’t many who present a lot complete help for the hacking of Linux machines.
In an e mail, Robinson mentioned Intezer discovered the malware on VirusTotal. He wrote:
The entity that submitted it seems to be associated to a Chinese language manufacturing organisation that makes small motor home equipment. We discovered this based mostly on different submissions from the identical submitter. I fingerprinted the server that we used to establish the corporate they usually had been certainly utilizing Centos (which the malware was compiled for). However this nonetheless shouldn’t be stable sufficient to conclude that they had been the targets or contaminated with the malware. We’ve got not discovered something new because the publication. The best factor which we hope to search out is among the encrypted malleable C2 configuration profiles. It will give us community IOCs to carry out pivoting off.
Intezer was in a position to get hold of elements of the framework however not every little thing. From the recordsdata the corporate researchers had been in a position to analyze, they may infer the presence of different modules. The corporate offered the next overview:
| Title | Title on Disk | Description |
| Lightning.Downloader | kbioset | The persistent module that downloads the core module and its plugins |
| Lightning.Core | kkdmflush | The principle module of the Lightning Framework |
| Linux.Plugin.Lightning.SsHijacker | soss | There’s a reference to this module however no pattern discovered within the wild but. |
| Linux.Plugin.Lightning.Sshd | sshod | OpenSSH with hardcoded non-public and host keys |
| Linux.Plugin.Lightning.Nethogs | nethoogs | There’s a reference to this module however no pattern discovered within the wild but. Presumably the software program Nethogs |
| Linux.Plugin.Lightning.iftop | iftoop | There’s a reference to this module however no pattern discovered within the wild but. Presumably the software program iftop |
| Linux.Plugin.Lightning.iptraf | iptraof | There’s a reference to this module however no pattern discovered within the wild but. Presumably the software program IPTraf |
| Linux.Plugin.RootkieHide | libsystemd.so.2 | There’s a reference to this module however no pattern discovered within the wild but. LD_PRELOAD Rootkit |
| Linux.Plugin.Kernel | elastisearch.ko | There’s a reference to this module however no pattern discovered within the wild but. LKM Rootkit |
To date there aren’t any identified cases of the Lightning Framework being actively used within the wild. Then once more, given the abundance of obtainable capabilities, state-of-the-art stealth is undoubtedly a part of the bundle.