[ad_1]

Getty Photographs
Researchers on Friday stated that hackers are exploiting the not too long ago found SpringShell vulnerability to efficiently infect susceptible Web of Issues gadgets with Mirai, an open supply piece of malware that wrangles routers and different network-connected gadgets into sprawling botnets.
When SpringShell (also referred to as Spring4Shell) got here to gentle final Sunday, some reports in contrast it to Log4Shell, the essential zero-day vulnerability within the well-liked logging utility Log4J that affected a large portion of apps on the Web. That comparability proved to be exaggerated as a result of the configurations required for SpringShell to work had been under no circumstances frequent. So far, there aren’t any real-world apps recognized to be susceptible.
Researchers at Pattern Micro now say that hackers have developed a weaponized exploit that efficiently installs Mirai. A blog post they printed didn’t determine the kind of system or the CPU used within the contaminated gadgets. The publish did, nonetheless, say a malware file server they discovered saved a number of variants of the malware for various CPU architectures.
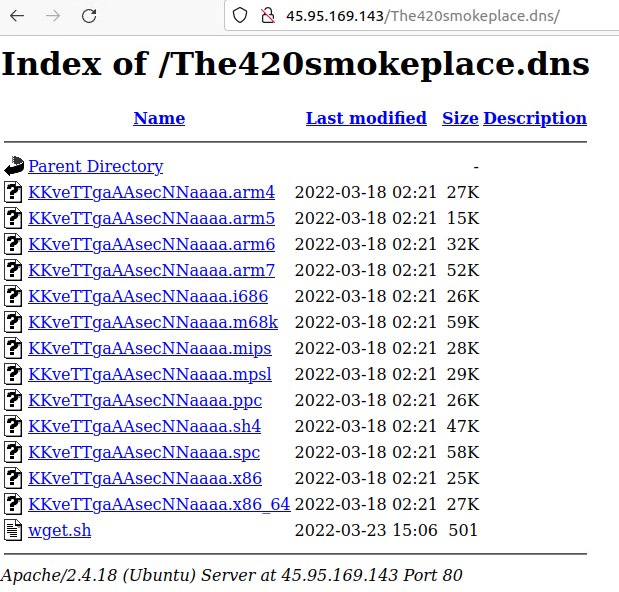
Pattern Micro
“We noticed lively exploitation of Spring4Shell whereby malicious actors had been in a position to weaponize and execute the Mirai botnet malware on susceptible servers, particularly within the Singapore area,” Pattern Micro researchers Deep Patel, Nitesh Surana, and Ashish Verma wrote. The exploits permit risk actors to obtain Mirai to the “/tmp” folder of the system and execute it following a permission change utilizing “chmod.”
The assaults started showing in researchers’ honeypots early this month. Many of the susceptible setups had been configured to those dependencies:
- Spring Framework variations earlier than 5.2.20, 5.3.18, and Java Improvement Package (JDK) model 9 or greater
- Apache Tomcat
- Spring-webmvc or spring-webflux dependency
- Utilizing Spring parameter binding that’s configured to make use of a non-basic parameter sort, equivalent to Plain Previous Java Objects (POJOs)
- Deployable, packaged as an online software archive (WAR)
Pattern stated the success the hackers had in weaponizing the exploit was largely as a consequence of their ability in utilizing uncovered class objects, which provided them a number of avenues.
“For instance,” the researchers wrote, “risk actors can entry an AccessLogValve object and weaponize the category variable ‘class.module.classLoader.assets.context.dad or mum.pipeline.firstpath’ in Apache Tomcat. They’ll do that by redirecting the entry log to put in writing an online shell into the net root via manipulation of the properties of the AccessLogValve object, equivalent to its sample, suffix, listing, and prefix.”
It’s arduous to know exactly what to make of the report. The shortage of specifics and the geographical tie to Singapore might recommend a restricted variety of gadgets are susceptible, or probably none, if what Pattern Micro noticed was some device utilized by researchers. With no thought what or if real-world gadgets are susceptible, it’s arduous to offer an correct evaluation of the risk or present actionable suggestions for avoiding it.